Sam Croley, a security researcher, posted a benchmark showing just how fast Nvidia’s new flagship GPU was. What was the benchmark? hashcat, a password recovery tool. However, it was used to see just how fast a 4090 could hash every combination of 8 characters (the most common length for passwords), including special characters. However, hashing all these character combinations is not the same as comparing and matching passwords.
This kind of direct hacking also requires a physical connection – they must have their rig present or a fast, direct connection to the device being hacked. That is likely to raise some eyebrows. Why? You need a beefy (likely heavy) rig and electrical connection.
Walking into any building with a massive brick of a suitcase is likely to get noticed.
Show Me The Money!
Nvidia’s new cards are not cheap. Each one has a manufacturer-suggested retail price (MSRP) of $1,600… so eight of them will total $12,800! That’s assuming supply chain issues don’t cause them to be scalped by third parties on the Internet. At that price, the average Internet user is not likely the intended target (see “Who’s Most At Risk?” below).
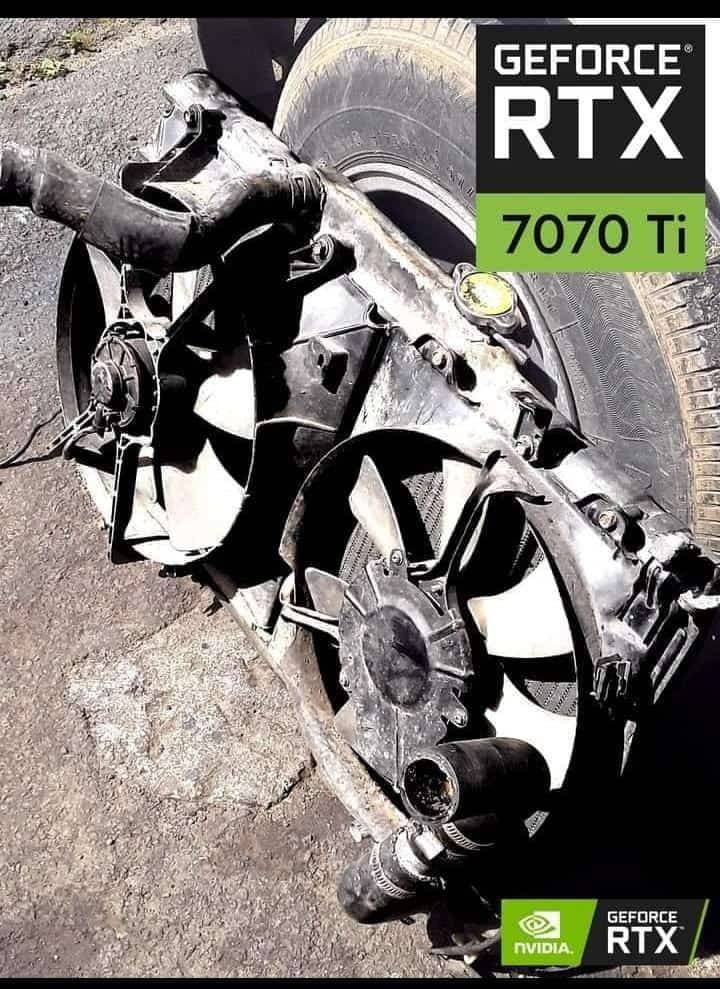
Hungry For Power

Nvidia’s RTX 4090 – just a single card – requires 450 watts and they recommend having a minimum 700 watt power supply (though they encourage 800 or more). However, to achieve the speeds tested, you need to overclock (OC) – make the card run commands faster than intended. That requires even more energy. While the researcher didn’t note energy requirements, other articles note seeing OC’ed 4090s claiming 616 watts for a single card.
Even at those power levels, it is likely to take days to go through all those character combinations with a single GPU. So how much would eight of them need? Well, simple math: eight RTX 4090s multiplied by 616 watts gives us a staggering 4,912 watts just for the cards alone. Add in the rest of a computer and you’re likely looking at roughly a 5,300 watt requirement!
That kind of power is going to require an isolated 240-volt circuit at 25 amps (about 6,000 total watts), and even then you’re within the cautionary limits of that breaker. While easy to find such a circuit in a data center, if you have to unplug something already present, it’s likely someone is going to notice. If you plug into a circuit that is not isolated, you could trip a breaker or blow a fuse – also likely someone will notice.
Firewalled
What about cracking across the internet? An increasing number of websites, small and large, are behind increasingly sophisticated barriers. These firewalls, some even using artificial intelligence (AI), often detect intrusion attempts and will automatically block them.
Who’s Most At Risk?
Given the bulk, money, and power requirements, the average Internet netizen is not likely to be a target. Other, higher-profile companies, organizations, governments, and individuals where the likelihood of a return on investment are most at risk. However, this brings up a few current and future concerns.
Public Figures
Every day, celebrities, politicians, government officials, executives, and IT professionals of the largest companies receive attacks. Attempts at phishing, malware, and ransomware attacks are common. Acquiring a stolen or improperly disposed of device periodically occurs. Use of common or guessable passwords. Accessing unencrypted networks. These scenarios are common, and faster technology makes it easier for attackers to gain access to personal & sensitive data.
Infrastructure
As warfare moves to cyberspace, infrastructure is increasingly a target. Fossil fuel production and electrical generation are required for companies and governments to compete. Making it easier to potentially break into will just put a larger target on them. Lare portions are aging and not kept up to date with the latest technology, which opens up the potential for vulnerabilities to be exploited.
Encryption Keys & Hashes
Over time, as technology gets faster, it decreases the effectiveness of encryption keys and hash algorithms. As they become obsolete, they are retired in favor of more complex keys that take greater amounts of processing power to break. Unfortunately, it also takes industries a while to update to more secure keys. This leaves many open to attack.
Will this advancement lead to algorithms being deprecated or retired? Not even close. Supercomputers just a few years ago would require up to 14 billion years to crack 128-bit AES encryption at 10.51 pentaflops. Today, the fastest supercomputer in the world, at 1.102 exaflops, would take nearly 10 billion years (generously).
How fast would eight 4090s be? Each one clocks in at 82.58 teraflops. Combined, 660 teraflops. Overclocked, they would be faster, but only to about 100 teraflops. Even combined at 800 teraflops, that is still only slightly more than half (0.8) a pentaflop – or about 7% the performance of supercomputers a few years back.
Suspects
Law enforcement attempts breaking into the devices of suspects – either through coercion, encryption-breaking tools, man-in-the-middle, and brute force attacks. Sometimes they ask or attempt to force the manufacturer or software developer of the device to assist. However, having a device capable of breaking into a device faster is just what law enforcement seeks.
In The End
Are you at risk? If you’re not a public figure, probably not. That being said, dumps of encrypted or hashed data will probably become a bigger target. Being able to decrypt large caches faster will mean large blocks of stolen information, which can include passwords, will increase everyone’s risk. I recommend updating your passwords (using longer than 8… better yet, longer than 16 characters), not reusing passwords (use a password manager), and enabling multi-factor authentication on accounts that support it.
Make it a habit to reset the passwords of your major accounts at least once a year. There are already national/international days for changing and enhancing your passwords. Add them to your own calendar.
Leave a Reply